This tutorial weblog examines a number of the use circumstances of key-value pair extractions, the normal and present approaches to fixing the duty, and a pattern implementation with code.
You encounter KVPs extra typically than you may understand. Bear in mind the final time you flipped by means of a dictionary? Every phrase (the important thing) is paired with its definition (the worth). Or take into account the varieties you have stuffed out – the questions are the keys, and your solutions are the values. Even within the enterprise world, invoices use this construction: gadgets bought are the keys, with costs as their corresponding values.
However here is the problem: in contrast to neatly structured tables, KVPs typically conceal in unstructured knowledge or unfamiliar codecs. Generally, they’re even partially handwritten. Think about making an attempt to manually extract knowledge from 1000’s of handwritten varieties or scanned invoices. It is a recipe for errors and frustration.
That is the place automated key-value pair extraction helps. By leveraging deep studying methods, we will educate machines to grasp doc buildings and extract worthwhile info precisely and effectively.
On this information, we’ll have a look at key-value pair extraction, from its wide-ranging purposes to cutting-edge methods. We’ll present an outline of KVP extraction use circumstances, assist you perceive conventional strategies and their limitations, discover how deep studying is revolutionizing the sphere, and information you thru constructing your personal extraction system.

Quick-track your KVP extraction with out compromising accuracy.
Constructing a customized key-value extraction system requires important time, experience, and sources. With Nanonets, you get ready-to-use fashions that deal with numerous paperwork, releasing you to concentrate on integrating knowledge into your workflows.
What’s a Key-Worth Pair (KVP)?
Think about you are organizing your closet. You may label every shelf: “Shirts,” “Pants,” “Sneakers.” These labels are your keys, and the gadgets on every shelf are the values. That is the essence of a key-value pair!
On the earth of information, a key-value pair (KVP) is a set of two linked knowledge parts: a novel identifier (the important thing) and its related knowledge (the worth). It is like a digital labeling system that permits for environment friendly storage and retrieval of knowledge.
KVPs are the constructing blocks of many knowledge buildings and databases. The fantastic thing about KVPs lies of their simplicity and suppleness. They’ll deal with structured knowledge (like spreadsheets) and unstructured knowledge (like textual content in paperwork) equally properly. This makes them a robust device for key info extraction from numerous sources.
Key-value pair extraction is not only for tech wizards. This highly effective method has purposes that stretch far past the realm of coding and knowledge science.
Let’s discover how KVP extraction is usually a game-changer for each private and enterprise use.
Private use circumstances

Whereas automation is generally used for large-scale productions, quick and correct key-value extraction can even profit small events and private usages, enhancing the group and effectivity of each day routines.
1. ID-scanning and knowledge conversion:
Private IDs are typical examples of paperwork that include numerous KVPs, from the given identify to the date of delivery. When wanted for on-line purposes, we frequently need to manually discover and sort within the info, which may very well be tedious and repetitive.
KVP extractions from pictures of the ID can enable us to rapidly convert knowledge into machine-understandable texts. Discovering the matching fields for various values will then turn into a trivial activity for applications, and the one handbook effort required could be to only scan by means of for double-checking.
2. Bill knowledge extraction for budgeting:
Budgeting is a vital side of our private routine. Whereas the event of Excel and spreadsheets has already made such irritable duties less complicated, a KVP extraction of things bought and their corresponding costs from merely a picture of the bill can pace up all the course of even quicker. Structured knowledge and numbers can enable us to rapidly carry out evaluation and be careful for purchases which can be past our affordability.
3. E-mail group and prioritization:
Drowning in a sea of emails? KVP extraction can assist you keep afloat. By figuring out key info like sender, topic, and vital dates inside emails, it will possibly routinely kind and prioritize your inbox. Think about by no means lacking an vital deadline or follow-up once more!
Companies use circumstances
Each industries and firms take care of 1000’s of paperwork with related codecs on daily basis. From purposes to asset administration, these doc info retrieval processes are sometimes labor-intensive.

Therefore, automation of the preliminary step of extracting key-value pairs inside unformatted knowledge can considerably scale back the redundancy of human sources whereas concurrently guaranteeing the reliability of the info retrieved.
1. Automation of doc scanning:
Governments or giant companies resembling banks course of many handwritten varieties with similar codecs for numerous functions (e.g., Visa software, financial institution switch). Retrieving the handwritten info from the varieties and changing it into digital paperwork by way of human effort may very well be extraordinarily repetitive and tedious, resulting in frequent minor errors.
A correct KVP extraction pipeline of changing handwritten knowledge into corresponding values of various keys after which inputting it into large-scale programs can scale back such errors and save further labor expenditures.
2. Survey assortment and statistical evaluation:
Firms and Non-Governmental Organisations (NGOs) could typically require suggestions from prospects or residents to enhance their present merchandise or promotional plans. They’d have to carry out a statistical evaluation to guage the enter comprehensively.
But, the same downside of changing unstructured knowledge and handwritten surveys into numerical figures that may very well be used for calculations nonetheless exists. Therefore, KVP extraction performs an important position in changing pictures of those surveys into analyzable knowledge.
3. Provide chain administration:
Within the advanced world of logistics, KVP extraction is usually a lifesaver. Extract key info from delivery manifests, invoices, and customs paperwork to streamline your provide chain processes. This could result in quicker shipments, diminished errors, and happier prospects.
4. Healthcare document administration:
For healthcare suppliers, managing affected person data effectively is essential. KVP extraction can assist digitize and set up affected person info from numerous sources – consumption varieties, lab studies, and physician’s notes. This not solely saves time however can even enhance affected person care by making crucial info simply accessible.
5. Authorized doc evaluation:
Regulation companies take care of mountains of paperwork each day. KVP extraction can assist legal professionals rapidly determine key info in contracts, court docket paperwork, and case recordsdata. This could considerably pace up case preparation and contract overview processes, permitting authorized professionals to concentrate on technique reasonably than drowning in paperwork.
6. Customer support optimization:
By extracting key info from buyer emails, chat logs, and assist tickets, companies can rapidly categorize and prioritize buyer points. This results in quicker response occasions, extra personalised service, and in the end, greater buyer satisfaction.
So, how precisely does KVP extraction work? And how will you implement it in your personal tasks or enterprise processes? Within the subsequent part, we’ll have a look at the normal approaches to KVP extraction and their limitations.
Put info extraction on autopilot now!
Get pre-trained fashions for doc varieties resembling invoices and receipts. This lets you quickly deploy KVP extraction with out in depth in-house growth.
Crucial ingredient of KVP extraction and discovering the underlying helpful knowledge is the Optical Character Recognition (OCR) course of. In easy phrases, OCR is the digital conversion of scanned pictures and images into machine-encoded texts for additional computations.
Earlier than the accuracy of deep studying meets the wants of the markets for such duties, OCRs are carried out with the next process:
- Database creation: First, we construct an enormous library of identified characters and symbols. It is like making a digital alphabet ebook.
- Function detection: When a picture is available in, OCR makes use of a photosensor to determine key factors and options. Think about tracing the traces of every letter along with your finger.
- Sample matching: The system then compares the detected options with its database of identified characters.
- Textual content conversion: Primarily based on the best similarity attributes, it transforms the matched patterns into machine-readable textual content, making your scanned picture or doc digitally accessible.
For years, this strategy has been the go-to methodology for extracting key-value pairs from paperwork. However as with all know-how, it has its limitations.
- Template dependence: Conventional strategies typically require predefined templates or guidelines for various doc varieties.
- Handwriting detection: Whereas nice with printed textual content, these programs typically stumble when confronted with the wild world of human handwriting.
- Lack of context: Conventional OCR focuses on particular person characters, typically lacking the larger image of how info is structured on the web page.
- Inflexibility: Adapting to new doc codecs or layouts will be time-consuming and require handbook updates to the system.
Regardless of these limitations, conventional strategies nonetheless play an important position in lots of key worth extraction eventualities. Nevertheless, as our knowledge wants have grown extra advanced – consider the huge array of doc varieties a big company offers with each day – so too have our extraction strategies.
Fortunately, the latest developments in deep studying have breathed new life into OCR and key-value pair extraction methods. Deep studying fashions, notably convolutional neural networks (CNNs), have revolutionized the sphere of picture recognition and textual content extraction.
Deep studying in motion
Deep studying is without doubt one of the important branches of machine studying that has gained reputation in latest many years. In contrast to conventional laptop science and engineering approaches, the place we design the system that receives an enter to generate an output, deep studying hopes to depend on the inputs and outputs to design an intermediate system that may be prolonged to unseen inputs by making a so-called neural community.
A neural community is an structure that’s impressed by the organic operate of the human mind. The community consists of a number of layers:
- Enter layer: That is the place your doc enters the system. Whether or not it is a scanned bill, a handwritten kind, or a digital PDF, the enter layer processes the uncooked knowledge.
- Hidden layers: These are the mind’s powerhouse. A number of layers work collectively to determine options, acknowledge patterns, and make sense of the doc’s construction.
- Output layer: That is the place the magic occurs. The system produces the extracted key-value pairs, neatly organized and prepared to be used.
Because the capability of GPUs and reminiscences drastically superior, deep studying has turn into a good technique in recent times, which ignited inventive variations of neural networks. One of the crucial typical neural networks used at this time, particularly in laptop imaginative and prescient, is the convolutional neural community (CNN). CNNs are convolutional kernels that slide by means of the picture to extract options, typically accompanied by conventional community layers to carry out duties resembling picture classification or object detection.

Get extremely correct KVP extraction as a service!
With Nanonets, you get state-of-the-art fashions by means of user-friendly APIs, enabling you to learn from AI-powered extraction with out the necessity to construct and keep advanced fashions in-house.
It would not simply have a look at particular person phrases or characters; it examines all the doc, contemplating format, font sizes, and even refined visible cues. This holistic strategy permits it to grasp the doc’s construction and extract key-value pairs with exceptional accuracy.
As an example, in healthcare document administration, a CNN can distinguish between affected person info, physician’s notes, and take a look at outcomes, even when the format varies between paperwork. This degree of understanding was merely not doable with conventional strategies.
Probably the most thrilling bit is that the extra paperwork a deep studying system processes, the smarter it turns into.
Now that you’ve some primary understanding of deep studying, let’s undergo a number of deep studying approaches for KVP extraction.
Tesseract OCR Engine
Current OCR methods have additionally included deep studying fashions to attain greater accuracy. The Tesseract OCR engine, maintained by Google, is a chief instance. It makes use of a particular kind of neural community known as Lengthy Brief-Time period Reminiscence (LSTM).
What’s LSTM?
An LSTM is a specific household of networks which can be utilized majorly to sequence inputs. This is why it is a game-changer for key worth pair extraction:
Sequential Knowledge Processing: LSTMs excel at dealing with sequential knowledge. Consider it as studying a doc the way in which a human would – understanding context and predicting what may come subsequent.
Context issues: In OCR, beforehand detected letters can assist predict the subsequent ones. For instance, if “D” and “o” are detected, “g” is extra more likely to observe than “y”.
Tesseract Structure
A small bounding field is moved ahead pixel by pixel with time. The picture bounded by the field is extracted to cross by means of each a ahead and backward LSTM, adopted by a convolution layer for the ultimate output.
The improved structure will increase the accuracy and robustness of the OCR, making it simpler to transform a number of various kinds of texts into one structured, digital doc. These digital paperwork with machine-readable strings are a lot simpler to be organised for KVP extraction.
Deep Reader
Apart from main the developments in OCR, deep studying additionally created alternatives for exploration. Deep Reader, a workshop paper from the highest CS convention ACCV*, is one instance that makes use of neural networks to acknowledge shapes and codecs extending past simply phrases and symbols of a scanned doc. Such methods will be notably useful in duties resembling KVP extraction.
*Facet Word: One of the best analysis papers from the pc science area are often revealed in top-tier conferences. Acceptance into such conferences symbolises an approval and recognition of by consultants inside the subject. The Asian Convention on Pc Imaginative and prescient (ACCV) is without doubt one of the acknowledged conferences inside the area of laptop imaginative and prescient.
What’s Deep Reader?
Whereas Tesseract focuses on textual content, Deep Reader takes key worth pair extraction to the subsequent degree by understanding all the doc construction.
Deep Readers makes an attempt to sort out the continued downside of inadequate info retrieval when extracting solely phrases and texts alone by additionally discovering the visible entities resembling traces, tables, and bins inside these scanned paperwork.
For each picture, Deep Reader denoises the picture, identifies the doc, and processes the handwritten textual content with a deep-learning strategy earlier than detecting and extracting significant texts and shapes. These options are then used to retrieve tables, bins, and, most significantly, KVPs.
Pre-processing
Previous to extracting textual entities, Deep Reader performs a number of pre-processing steps to make sure the highest quality retrieval within the latter components:
- Picture de-noising: Deep Reader adopts a generative adversarial community (GAN) to generate a de-noised model of an enter. GAN, first developed by Ian et al. in 2014, is a neural community that includes two sub-networks — a generator and a discriminator. As soon as an enter is given, the generator generates a picture based mostly on the enter, and the discriminator tries to differentiate between the bottom reality and the generated enter. Upon training-completion, a generator can efficiently generate a picture based mostly on the enter that’s near the precise floor reality. On this case, the GAN, given pairs of pictures (one de-noised and one noised), makes an attempt to learn to generate the de-noised model of the picture from the perturbed one.
- Doc identification: In an effort to precisely retrieve visible entities, Deep Reader additionally makes an attempt to categorise the scanned paperwork into one of many templates by way of a convolutional Siamese community. The Siamese community consists of two similar convolutional layers that settle for pictures of the scanned doc and templates as inputs respectively, then compute the similarity between the 2. The very best similarity amongst all comparisons implies that the doc is predicated on the template.
- Processing handwritten textual content: To sort out the issue of recognising handwritten texts, Deep Reader additionally adopts a handwritten textual content recognition by means of an encoder-decoder to map the handwritten texts into units of characters.
Deep Reader Structure
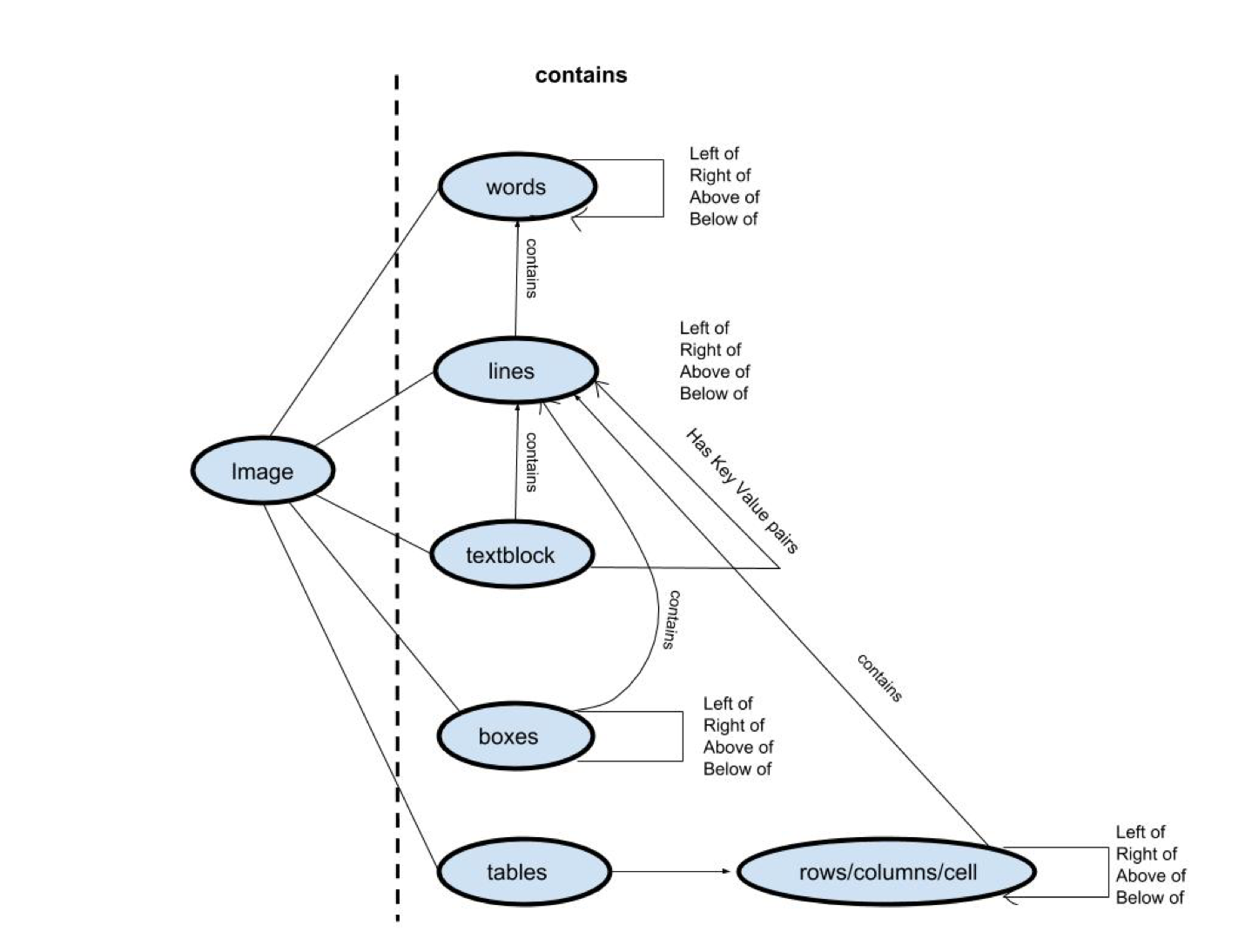
After pre-processing, Deep Reader detects a set of entities from the picture, together with web page traces, textual content blocks, traces of textual content blocks, and bins. The detection goes by means of the schema, as proven within the above determine to retrieve a complete set of information from the scanned doc.
Rule-based strategies offered by area consultants are additionally adopted to assist the extraction course of. For instance, Deep Reader makes use of summary common knowledge varieties resembling metropolis, nation, and date to make sure that the fields retrieved are related.
Let’s apply our theoretical data to a sensible downside. We’ll concentrate on a typical but difficult state of affairs: extracting firm, handle, and value fields from invoices. Whether or not you are a small enterprise proprietor monitoring bills or an information scientist automating doc processing, this implementation gives you a stable basis.
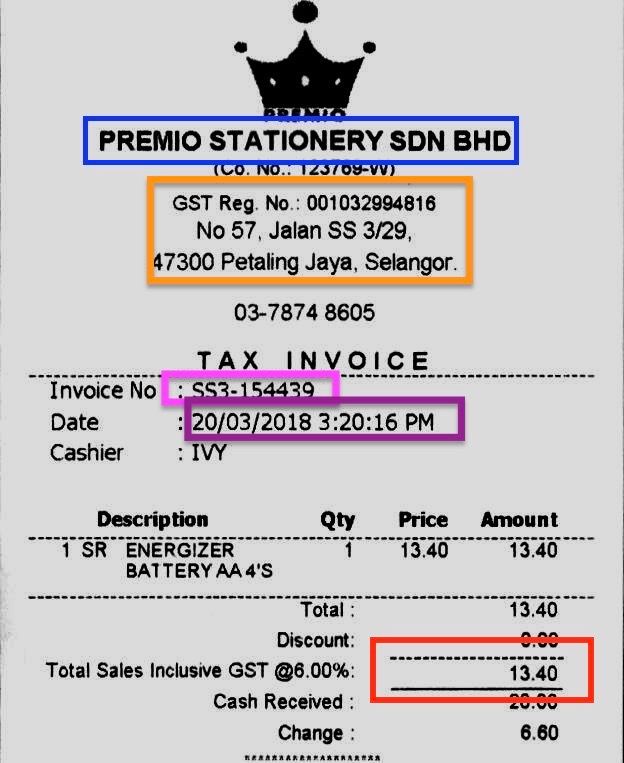
The determine above is a typical bill template saved in a picture format. We now have many of those invoices with related codecs, however manually discovering the KVPs, resembling the corporate identify, handle, and complete value, is a tiring job. Thus, the intention is to design a KVP extractor such that with a given format (or related codecs), we will routinely retrieve and current the KVPs.
To carry out KVP extraction, we’ll want an OCR library and a picture processing library. We’ll use the notorious openCV library for picture studying and processing and the PyTesseract library for OCR. The PyTesseract library is a wrapper of the aforementioned Google Tesseract engine, which can be adequate for our activity.
*Facet Word: This system is predicated on the answer of the ICDAR Robusting Studying Problem
Half I — Libraries
You need to use pip to put in the 2 libraries by way of the next instructions:
https://gist.github.com/ttchengab/c040ab7ce44114d76c63ecef226d5d09
After set up, we will then import the libraries as the next:
https://gist.github.com/ttchengab/cd32bcd502e99c3e3cc9c73f693927c7
We may also need to import some exterior libraries:
https://gist.github.com/ttchengab/01280236448e4fc4a03505f6f0baea3f
Half II — Picture Preprocessing
https://gist.github.com/ttchengab/293fc3ca782b20cf9b05c33f13583338
The operate above is our picture preprocessing for textual content retrieval. We observe a two stage strategy to perform this:
Firstly, we make the most of the cv2.imread() operate to retrieve the picture for processing. To extend the readability of the texts within the picture, we carried out picture dilation adopted by noise removing utilizing some cv2 features. Some extra features for picture processing can be listed within the remark part. Then, we discover contours from the picture and based mostly on the contours we discover the bounding rectangles.
Secondly, after picture processing, we then iteratively retrieve every bounding field and use the pytesseract engine to retrieve retrieve all of the textual content info to feed right into a community for KVP extraction.
https://gist.github.com/ttchengab/b81ea8bb1c21121237845d65d15aa3a0
The mannequin above is an easy LSTM that takes the texts as inputs and outputs the KVPs of firm identify, date, handle, and complete. We adopted the pre-trained mannequin from the answer for testing.
The next are the analysis features for the LSTM community with a given set of texts:
https://gist.github.com/ttchengab/9f31568ef1b916ab0ee74ac1b8b482e5
Half IV – Whole Pipeline
https://gist.github.com/ttchengab/c2f7614cbeaa8cd14883d4ebbcd36ba6
With all of the features and libraries applied, all the pipeline of KVP extraction will be achieved with the above code. Utilizing the bill above, we may efficiently retrieve the corporate identify and the handle as the next:

To check the robustness of our mannequin, we will additionally take a look at on invoices with unseen codecs, resembling the next:
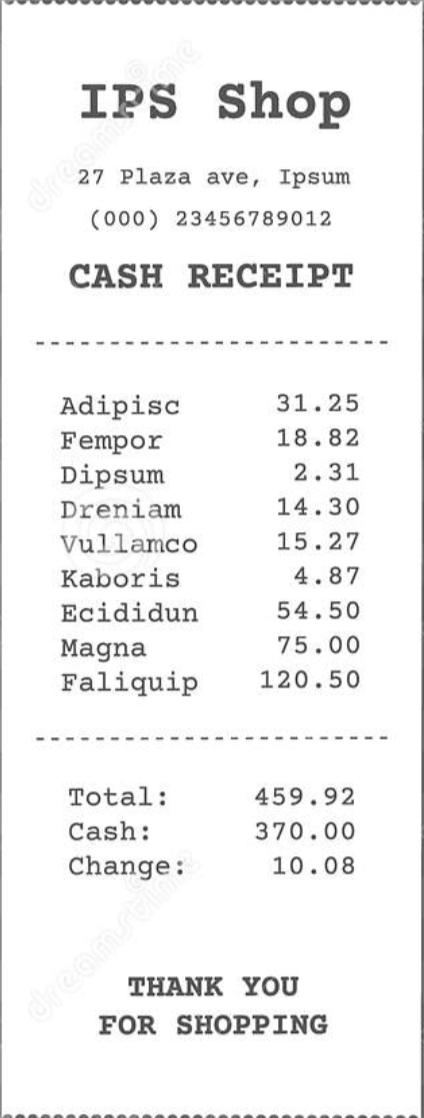
Through the use of the identical pipeline, with out additional coaching, we may get hold of the next:

Despite the fact that we could not retrieve different info resembling firm identify or handle, we had been nonetheless in a position to get hold of the whole appropriately with out ever seeing any related bill codecs earlier than!
With an understanding of the mannequin structure and pipeline, now you can use extra bill codecs which can be extra related as coaching and proceed to coach the mannequin in order that it might work with greater confidence and accuracy.
Finest practices and optimization methods for Key-Worth Extraction
Implementing an efficient key worth pair extraction system is not nearly writing code; it is about optimizing your strategy for accuracy, effectivity, and scalability. Listed here are some finest practices to supercharge your extraction course of:
- Clear your pictures: Take away noise, right skew, and improve distinction.
- Standardize codecs: Convert all paperwork to a constant format earlier than processing.
- Create customized dictionaries: Construct lists of anticipated keys for particular doc varieties.
- Use common expressions: Design patterns to catch frequent worth codecs (e.g., dates, forex).
- Validate extracted knowledge: Arrange checks to make sure extracted values make sense.
- Deal with exceptions: Plan for sudden doc codecs or OCR errors.
- Use parallel processing: Distribute extraction duties throughout a number of cores or machines.
- Implement caching: Retailer incessantly accessed knowledge to cut back processing time.
- Implement suggestions loops: Allow customers to right errors, feeding this knowledge again into your system.
- Commonly replace your fashions: Retrain on new knowledge to enhance accuracy over time.
- Encrypt delicate knowledge: Shield extracted info, particularly when coping with private or monetary particulars.
- Implement entry controls: Guarantee solely licensed personnel can entry extracted knowledge.
What’s a Key-Worth Database?
Whereas we have explored the intricacies of key worth pair extraction, it is essential to grasp the place this knowledge typically finally ends up: key-value databases. These highly effective programs assist many trendy purposes, from e-commerce platforms to social media networks.
A key-value database, also called a key-value retailer, is a sort of non-relational database that makes use of a easy key-value methodology to retailer knowledge. Every merchandise within the database is saved as an attribute identify (or “key”) along with its worth.
Key-Worth vs. Relational Databases
Conventional relational databases set up knowledge into tables with predefined schemas. In distinction, key-value databases supply extra flexibility:
- Schema-less: Key-value databases do not require a set schema, permitting for simple modifications.
- Scalability: They’ll deal with huge quantities of information and visitors extra effectively.
- Efficiency: For easy queries, key-value databases typically outperform relational databases.
As we have explored the complexities of key-value pair extraction, it is clear that implementing a strong answer requires important experience. That is the place platforms like Nanonets shine, providing a highly effective OCR API that simplifies the extraction course of.
Nanonets leverages cutting-edge AI to supply:
- Pre-trained fashions for frequent paperwork like invoices, receipts, and ID playing cards
- Customized coaching capabilities on your distinctive doc codecs
- Excessive accuracy on each printed and handwritten textual content
- Seamless integration by means of a RESTful API
- Versatile post-processing guidelines to refine extracted knowledge
For organizations seeking to rapidly implement key worth extraction with out compromising on high quality, Nanonets gives a compelling answer. By dealing with the complexities of AI mannequin growth and upkeep, Nanonets permits companies to concentrate on what actually issues – deriving worth from their doc knowledge.
Whether or not you are a startup processing your first batch of invoices or an enterprise dealing with hundreds of thousands of paperwork, platforms like Nanonets are making superior key worth extraction accessible and environment friendly.
Closing ideas
We have coated numerous floor on key-value pair extraction. We have explored the idea of KVPs, their use circumstances, and numerous extraction strategies – from conventional OCR to cutting-edge deep studying approaches. However bear in mind, there’s nonetheless an extended method to go.
This subject is consistently evolving, with AI and machine studying pushing the boundaries of what is doable. As we wrap up, take into account how one can apply these insights to your personal doc processing challenges.