Share this text
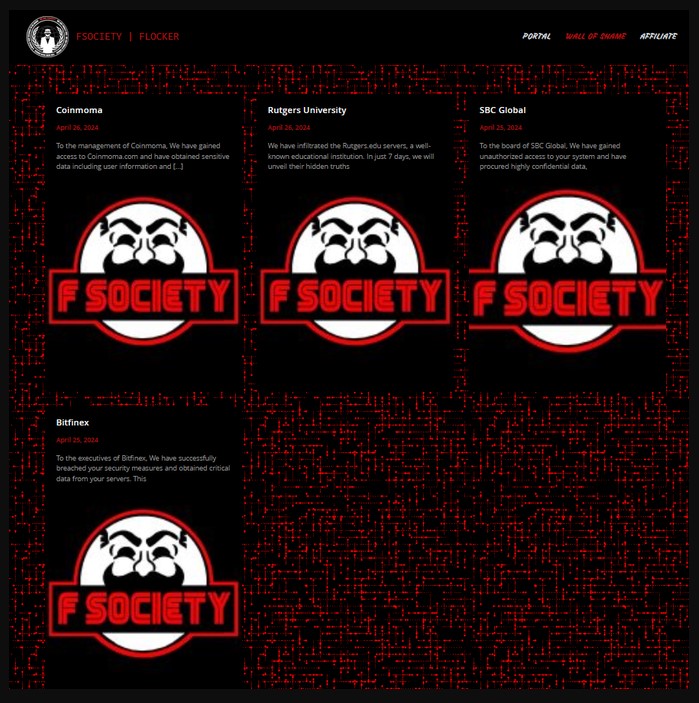
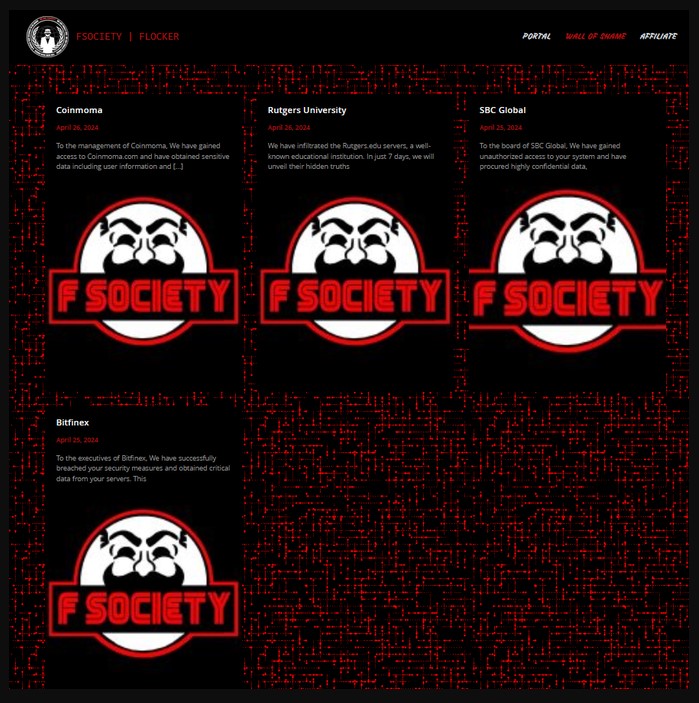
Bitfinex has been thrust into the highlight not too long ago after a ransomware group, named “FSOCIETY,” claimed to have gained entry to 2.5TB of the alternate’s knowledge and the private particulars of 400,000 customers. In response to the allegations, Bitfinex CTO Paolo Ardoino clarified that the claims of a database hack seem like “faux” and warranted consumer funds stay safe.
Ardoino discovered on the market have been knowledge discrepancies and consumer knowledge mismatches within the hacker’s posts.
The hackers posted pattern knowledge containing 22,500 data of emails and passwords. Nonetheless, in line with Paolo, Bitfinex doesn’t retailer plain-text passwords or two-factor authentication (2FA) secrets and techniques in clear textual content. Moreover, of the 22,500 emails within the leaked knowledge, solely 5,000 match Bitfinex customers.
In line with him, it might be a typical problem in knowledge safety: customers usually reuse the identical e mail and password throughout a number of websites, which could clarify the presence of some Bitfinex-related emails within the dataset.
One other spotlight is the dearth of communication from the hackers. They didn’t contact Bitfinex on to report this knowledge breach or to negotiate, which is atypical habits for ransomware assaults that usually contain some type of ransom demand or contact.
Furthermore, details about the alleged hack was posted on April 25, however Bitfinex solely turned conscious of the declare not too long ago. Paolo stated if there had been any real risk or demand, the hackers would have seemingly used Bitfinex’s bug bounty program or buyer assist channels to make contact, none of which occurred.
“The alleged hackers didn’t contact us. If they’d any actual data they’d have requested a ramson by way of our bug bounty, buyer assist ticket and many others. We couldn’t discover any request,” wrote Ardoino.
Bitfinex has carried out a radical evaluation of its methods and, up to now, has not discovered any proof of a breach. Paolo stated the crew would proceed to overview and analyze all obtainable knowledge to make sure that nothing is ignored of their safety assessments.
After information of a possible breach surfaced, Shinoji Analysis, an X consumer, confirmed the authenticity of the leak. The consumer stated he tried one of many passwords within the leaked data and obtained a 2FA.
Nonetheless, at press time, he eliminated his submit and corrected the earlier data.
Eliminated the unique BFX hack submit as I am not in a position to edit it. What seems to have occurred is that this “Flocker” group curated an inventory of BitFinex logins from different breaches.
They then made the location appear like a ransom demand for a significant breach.
— Alice (e/nya)🐈⬛ (@Alice_comfy) Might 4, 2024
In a separate submit on X, Ardoino steered that the true motive behind the exaggerated breach claims is to promote the hacking device to different potential scammers.
The concept is to generate buzz round these high-profile (Bitfinex, SBC World, Rutgers, Coinmoma) hacks to advertise their device, which they allege can allow others to hold out related assaults and doubtlessly make giant sums of cash.
Right here a message from a safety researcher (that as a substitute of panicking, making an attempt to dig a bit extra into it).
“I imagine I begin to perceive what is going on and why they’re sending these messages claiming you have been hacked.
The message within the screenshot within the ticket got here from a… pic.twitter.com/YjwG2eeXw2— Paolo Ardoino 🍐 (@paoloardoino) Might 4, 2024
Moreover, he questioned why the hackers would wish to promote a hacking device for $299 if they’d actually accessed Bitfinex and obtained precious knowledge.
Share this text





