On March 19, Trezor’s X suffered a safety breach that uncovered the account’s 200,000 followers to a pretend crypto presale. After the alarms have been raised, most crypto customers stayed vigilant whereas the {hardware} pockets firm regained management.
Trezor’s crew lately printed a preliminary report addressing the considerations. The submit additionally defined the flowery phishing rip-off that bypassed the corporate’s safety measures.
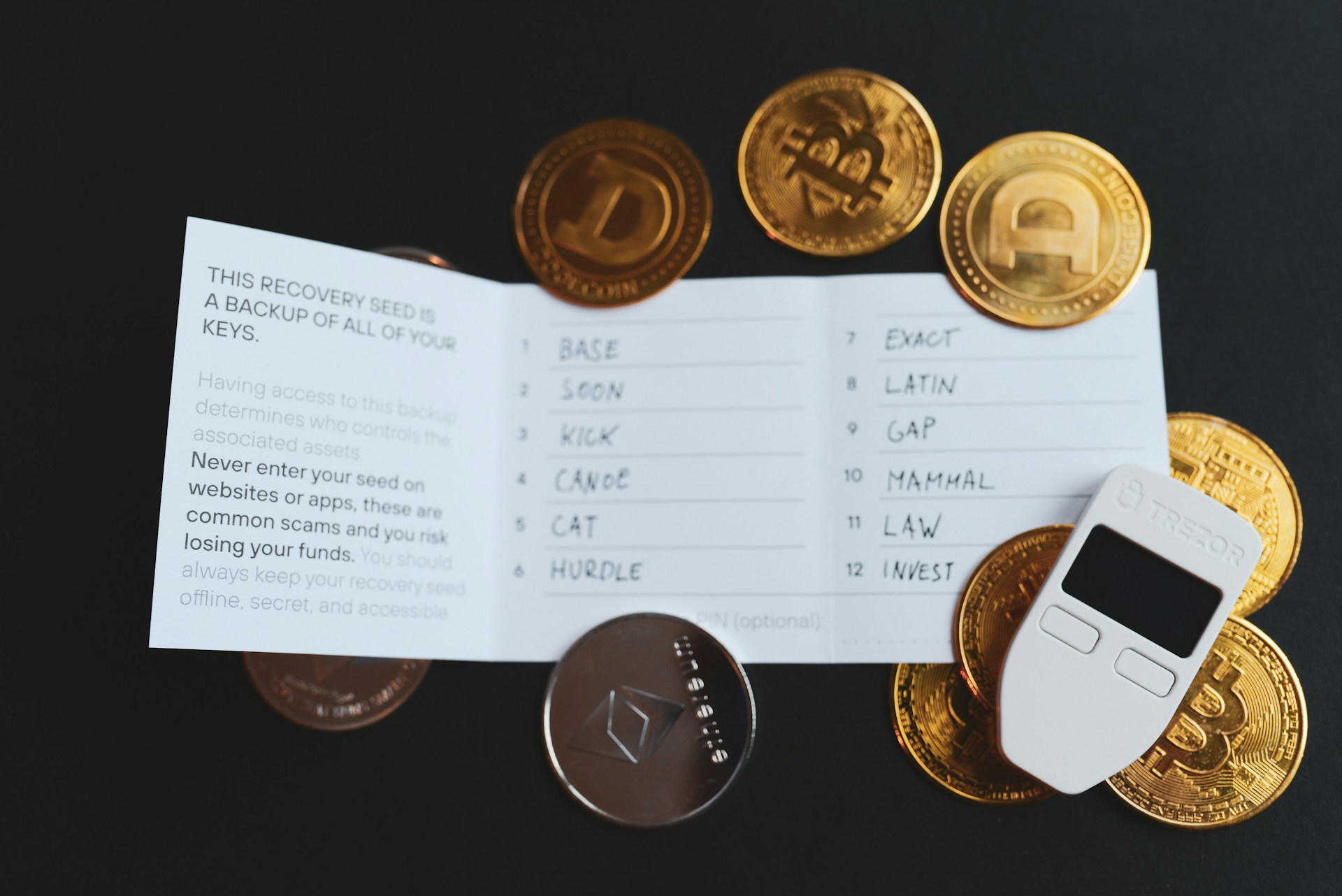
Is Trezor’s “Unwavering Safety” Nonetheless Defending Your Crypto?
After gaining management of the account, the hacker posted a pretend presale handle for a $TRZR token. Disguised as an “initiative” to assist the Slerf group, the submit provided a “separate bonus airdrop” from an internet site linked within the submit that redirected to a pockets drainer.
After Trezor regained management of the account, X customers expressed their worries in regards to the incident and urged that the hack was a “unhealthy look” on the security-focused firm. Nevertheless, the corporate assured that they’d “strong safety measures.”
We need to make clear that we don’t make use of SMS for 2FA, and as a substitute make use of safer strategies of authentication.
The corporate lastly addressed customers’ considerations in a preliminary report. The hack is feasible as a result of a “subtle phishing rip-off” as a substitute of an absence of fundamental safety measures.
The corporate is predicated on “unwavering safety,” the submit states; as such, all merchandise and inner methods stay unaffected regardless of the breach.
Assertion from Trezor's preliminary report. Supply: Medium.com
Refined Phishing Rip-off Steals Pocket Change
In response to Trezor, the continued investigation has revealed that “the breach seems to have arisen from a complicated and calculated phishing assault that was within the works for weeks.”
The calculated scheme started on February 29 after the attacker posed for a “credible entity” from the crypto trade. On the time of writing, the id of the impersonated determine was not revealed.
The attacker contacted Trezor’s PR crew via X utilizing a “well-crafted social media presence.” The seemingly real contact aimed to schedule an interview with the corporate’s CEO.
In response to the report, the attacker and the crew had a back-and-forth dialog over a number of days, which made the efforts to stage a name appear extra credible. Nevertheless, the decision settlement led to the press of the hyperlink that granted entry to Trezor’s X account.
The malicious hyperlink was disguised as a Calendly invite that, upon clicking, redirected a Trezor’s crew member to a web page requesting the X login credentials. The crew rescheduled the decision because the incident raised crimson flags.
In the course of the rescheduled name, the attacker pretended to have technical points and urged Trezor’s crew member “to ‘authorize’ becoming a member of the decision.” This authorization related the hacker’s Calendly app with the corporate’s X account. Because of this, the attacker gained entry to the account and printed the now-deleted posts.
he bought a whopping 0.96 Solana as effectively pic.twitter.com/zqHjxM8EOI
— xc (@Theft) March 19, 2024
The hacker solely stole $8,100 from the malicious hyperlink redirecting to the pockets drainer. Impressively, simply 0.96 SOL (round $162,4 at writing time’s pricing) have been despatched to the pretend presale handle.
Undoubtedly, the assault was a calculated and elaborate scheme that aimed to develop into a giant heist. Nevertheless, the hacker’s try was halted by the crypto group surveillance and the suspicious nature of the unauthorized posts.

Bitcoin is buying and selling at $63,460 within the 3-day chart. Supply: BTCUSDT on Buying and selling.view.com
Featured Picture from Unsplash.com, Chart from TradingView.com