“Authorities brokers aren’t lively in Bitcoin developer and influencer circles.”
Because the battle for world financial supremacy wages on, you need to assume that the state is actively working data warfare. Which means the state is working and performing in an effort to protect and increase it’s personal energy. For that cause, it’s sane and affordable to imagine that state operators are within the trenches of Bitcoin trying to affect public notion, developer exercise, and general bitcoin adoption. In case you assume this isn’t occurring then you might be naive otherwise you’re incentivized to behave towards bitcoin otherwise. The sabotage of Bitcoin shouldn’t be some tin foil hat conspiracy, the sabotage of Bitcoin is actively taking part in out in actual time, however the massive query is the place the sabotage is happening and what are you able to do to determine and act to counter the sabotage?
So let’s zoom into Bitcoin of at the moment, the place dialog is occurring round the way forward for Bitcoin with regard to coping with Ordinals, or spam (if you’re a part of that camp)1. The rise of Ordinals final 12 months and the stress they’ve prompted on blockspace demand has surfaced new rivalries inside the bitcoin maximalist group as memetic warfare is waged on what bitcoin is and the way it must be used. The aim of this text shouldn’t be to make a political stand on this combat, however to level out locations in Bitcoin which might be liable to sabotage and the place lively sabotage campaigns is likely to be actively waged. Seeing this division in a as soon as divided entrance is sufficient to make one pause and think about what exterior forces are at work.
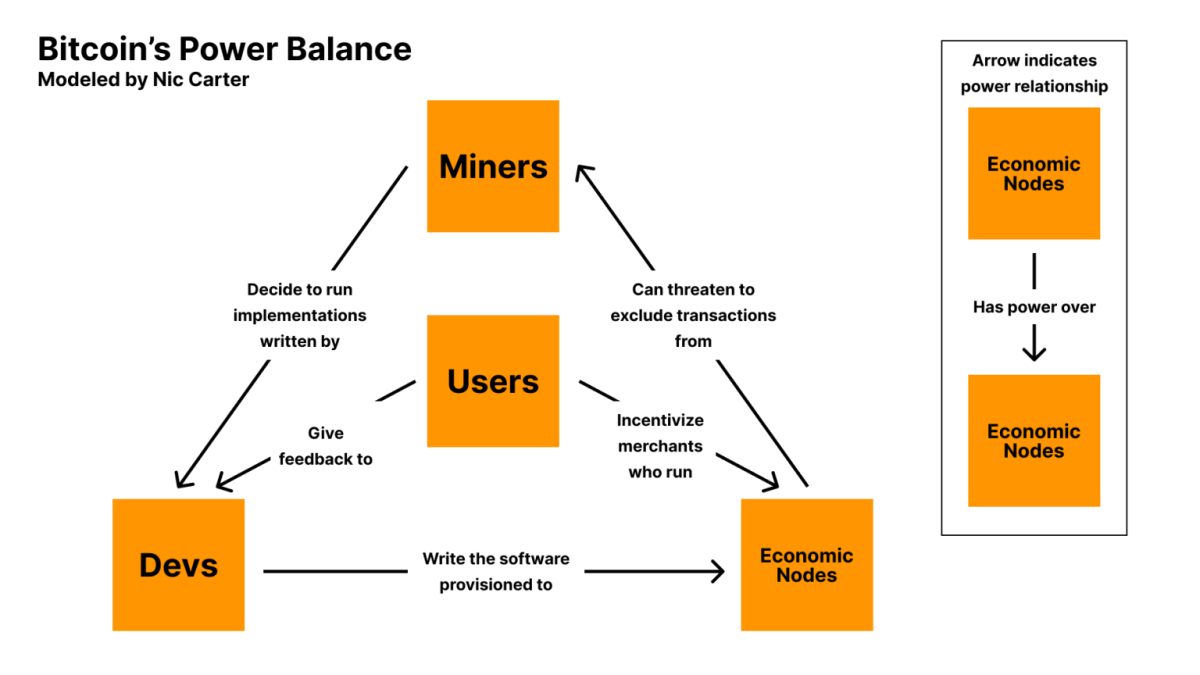
Bitcoin’s Energy Steadiness
As we think about the infighting occurring inside Bitcoin, it is very important perceive the totally different events inside bitcoin and the way every of the powers steadiness one another out. In 2019, Nic Carter illustrated Bitcoin’s Energy Steadiness Mannequin. This mannequin exhibits the important thing roles in Bitcoin and the connection between every one. You possibly can see the round suggestions loop between Miners -> Devs -> Financial Nodes. In a vacuum these three roles would perpetually pump one another with nothing to maintain them in test. On the coronary heart of the mannequin are the Customers who hold Devs and Financial nodes in test.
The one issue within the energy mannequin that touches every of the participant within the mannequin is the software program of code. The software program touches every of the roles in a technique or one other and that is in all probability the most important risk vector to all of Bitcoin. The easy exercise of operating code is how Bitcoin is consuming the financial world, so it’s in all probability price understanding the event course of.
Bitcoin Growth Course of
Let’s now dig into the Bitcoin growth course of. As you recognize, making adjustments to Bitcoin is a sluggish and deliberate course of. It is a massive change from the “transfer quick and break issues” mentality of Silicon Valley. Many argue that this sluggish methodical course of is definitely one in all Bitcoin’s best strengths. In 2011, Gwern revealed “Bitcoin Is Worse Is Higher” the place he says “Nonetheless, in an instance of ‘Worse is Higher’, the ugly inefficient prototype of Bitcoin efficiently created a safe decentralized digital forex, which might wait indefinitely for achievement, and this was sufficient to finally result in adoption, enchancment, and development right into a safe world digital forex.” This ugly inefficient code has gotten us right here at the moment, 15 years later, and in that point the sluggish methodical strategy to Bitcoin growth has been and can in all probability proceed to be part of the developer ethos.
The event course of has even been formally documented in BIP 2 (Bitcoin Enchancment Proposal). Listed here are the final steps within the BIP activation course of:
- Drafting the BIP: Step one is to draft a BIP following the template outlined in BIP2. This consists of writing an in depth doc or white paper that outlines the proposed adjustments. The BIP must be complete, overlaying motivation, technical specs, and rationale.
- Dialogue and Suggestions: As soon as the BIP is drafted, it’s shared with the Bitcoin group for dialogue and suggestions and normally occurs on platforms just like the Bitcoin Dev mailing record, GitHub, and even Twitter. The aim is to solicit suggestions, refine the proposal, and start to construct consensus round it.
- Assigning a BIP Quantity: If the BIP is deemed to have potential and is exclusive, it’s assigned a BIP quantity by a BIP editor. It is a formal acknowledgment that the BIP is into account.
- Formal Evaluate: After the BIP is assigned a quantity, it enters a proper evaluate section. Throughout this time, the BIP is scrutinized for technical soundness, feasibility, and compatibility with the Bitcoin protocol. That is the place the devs attempt to break the bip and poke holes within the proposal.
- Revisions: Based mostly on suggestions and evaluate, the BIP could endure a number of revisions.
- Implementation: As soon as consensus is reached, the BIP is applied within the Bitcoin Core codebase. This step entails precise coding and rigorous testing to make sure that the adjustments work as supposed with out introducing new vulnerabilities.
- Reaching Consensus: For a BIP to maneuver ahead, it wants to achieve consensus among the many Bitcoin growth group. That is usually probably the most difficult half, as Bitcoin’s decentralized nature implies that a variety of stakeholders (builders, miners, customers, and so forth.) must agree on the change.
- Deployment: After implementation & consensus, the brand new model of Bitcoin Core together with the BIP is launched. Relying on the character of the BIP, it’d require a majority of miners or nodes to improve to the brand new model for the adjustments to take full impact.
- Activation: Lastly, as soon as the required threshold of community individuals has adopted the brand new model, the adjustments proposed within the BIP are activated on the Bitcoin community.
Studying by means of that is extremely useful in understanding how change occurs to Bitcoin. The issue I see is the place are the one level of failures on this course of and who the gatekeepers2 are for every step. Conversations occurring in channels now are surfacing weak factors or non documented components of the event cycle. For instance, Bitcoin Inquisition. That is the in area between steps 2 and three.
Bitcoin Inquisition
Bitcoin Inquisition is a non-documented a part of the Bitcoin growth course of. It was proposed by and administered by AJ Cities in 2022. Here’s a very transient abstract of why and what it’s.
“I believe the weakest hyperlink in that [bitcoin development] loop is the primary one: what if we did activate comfortable forks on the default signet previous to the code being merged into core? To that finish, I’m proposing a fork of core that I’m calling “bitcoin-inquisition”, with the concept it branches from secure releases of core and provides help for proposed adjustments to consensus (CTV, ANYPREVOUT, TLUV, OP_CAT, and so forth…) and probably additionally relay coverage (relay adjustments are sometimes implied by consensus adjustments, but in addition probably issues like bundle relay).”
– AJ Cities on Bitcoin Inquisition
The fact is that the Bitcoin Inquisition is dwell and nicely. AJ runs a particular separate fork of Bitcoin core and acts as the only admin for testing BIP’s. This isn’t documented in BIP-2, however has simply been accepted as course of by core devs. It is a curious growth of how tribal devs could make adjustments how they see match, with out documentation.
The Bitcoin Sabotage
At this level we’ve run by means of the roles in Bitcoin, the steps within the growth course of, and even recognized a obtrusive gap within the growth course of. Let’s now dig into what’s sabotage.
Sabotage. (noun) /ˈsæb.ə.tɑːʒ/
Definition: The deliberate destruction, harm, or obstruction of one thing, sometimes for political or army benefit. Sabotage is commonly carried out covertly and with the intention of hindering operations, actions, or plans of an opponent or competitor.
Verb Kind: Sabotage (sabotaging, sabotaged)
Utilization in a Sentence: “The bridge collapse was discovered to be the results of sabotage by enemy brokers.”
For function of this text, let’s body sabotage particularly in relation to Bitcoin Sabotage. Bitcoin Sabotage is the deliberate destruction of Bitcoin, or obstruction of Bitcoin growth or adoption, for political benefit. That is the body. That is what we’re up towards. With that in thoughts let’s now dig into how sabotage is waged. Conveniently our very personal CIA is masters at sabotage and have been waging sabotage ways in warfare for over a century.
Easy Sabotage Discipline Guide
Within the 1940’s, the CIA shipped a area guide known as Easy Sabotage Discipline Guide. The aim of this was to distribute to operators a sensible guide on how one can conduct sabotage operations behind enemy traces. Whereas this guide is 80 years outdated, it reveals some classical ways within the artwork of sabotage.
This “Easy Sabotage” is a novel have a look at how sly the army is on the subject of unconventional warfare. This guide was developed within the 1940’s and you need to marvel what number of extra hours and sources have gone into modernizing this identical doc and different categorized operators manuals. For function of this text, we’ll look at the Particular Recommendations for Sabotage sections targeted on Organizations and Conferences & Managers and Supervisors.
- Organizations and Conferences
- Insist on doing all the pieces by means of “channels.” By no means allow short-cuts to be taken in an effort to expedite choices.
- Make “speeches,” Discuss as regularly as potential and at nice size., Illustrate your factors by lengthy anecdotes and accounts of private experiences. By no means hesitate to make just a few applicable patriotic” feedback.
- When potential, refer all issues to committees, for “additional examine and consideration.” Try to make the committees as massive as potential – by no means lower than 5.
- Carry up irrelevant points as regularly as potential.
- Haggle over exact wordings of communications, minutes, resolutions.
- Refer again to issues determined upon on the final assembly and try to re-open the query of the advisability of that call.
- Advocate “warning.” Be unreasonable” and urge your fellow-conferees to be “affordable” and keep away from haste which could lead to embarrassments or difficulties afterward.
- Be apprehensive in regards to the propriety of any resolution – increase the query of whether or not such motion as is contemplated Hes inside the jurisdiction of the group 01’whether or not it’d battle with the coverage of some greater echelon.
After I learn Part A. Organizations and Conferences, I can’t assist however assume that Bitcoin growth is being sabotaged, however I’m a naive outsider. I’m additionally a noticer. If I used to be going to sabotage Bitcoin, this area guide might simply be deployed from inside developer circles. In case you have been a state operator with growing abilities, it’s affordable to imagine you would start collaborating in code evaluate course of and make in roads and begin having authority in issues.
Let’s define sabotage ways state operators might be executing:
- Miners – within the nice blocksize wars, some massive mining swimming pools signaled with the Large Blockers. This was an assault on Bitcoin, nevertheless it demonstrates a particular motion that Mining Pool operators might perform in an effort to sabotage Bitcoin. Whereas this DID NOT work in breaking Bitcoin, we discovered that Customers are on the coronary heart of Bitcoin. A much bigger drawback might be if massive pool operators have been performing in coordination with different roles.
- Devs – that is maybe the largest vector for sabotage assault. As we see extra worth soaked up by Bitcoin, it can change into a much bigger goal for state actors. Which means we can have state operators submitting pull requests and collaborating within the growth course of. Based mostly on the Easy Sabotage Discipline Guide, operators might simply perform most of the ways outlined above. We’re already seeing very divisive positions from builders on how bitcoin must be, so you could marvel who’s the operator.
- Customers – since customers give suggestions to builders, you’d assume that giving unhealthy suggestions might result in builders constructing one thing that’s not in bitcoins greatest curiosity. Or customers might socially assault builders into doing sure issues. Proper now we’re seeing meme warfare being waged inside the maximalist group, and it could’t all be natural discourse. Customers infighting can result in maldevelopment. Additionally, what occurs if a gaggle of unhealthy actors within the customers and builders camps are aligned. Or what if customers coordinate to affect sure builders?
- Financial Nodes – they select what transactions make it to miners by way of the code they run. Customers inform them what code to run as a result of customers spend cash with them. Financial nodes might sabotage by supporting outdated code, or malicious sabotaged code.
In wrapping up this piece, the advanced dynamics between miners, devs, customers, and financial nodes inside Bitcoin creates a ripe battle floor for meme warfare and Bitcoin Sabotage. The Bitcoin growth course of is with out flaws and as outlined within the CIA’s Easy Sabotage Discipline Guide, there are a lot of easy to deploy ways that might be used to sabotage Bitcoin. This could function a sobering actuality that Bitcoin is below assault and you must act accordingly.
The duty is on you, humble frog, to maintain your head on a swivel. You could keep conscious and name out bullshit. Whether or not it’s combating gaslighting, finishing up moral trolling, or reviewing code, all these actions rely and assist protect our solely real looking shot at a extra free future. The survival and flourishing of Bitcoin rely not simply on NGU and its technological robustness however equally on the collective vigilance the customers. As we navigate these unsure instances, allow us to be guided dedication to cypherpunk ethos, essential pondering, and unwavering help for the core rules that underpin Bitcoin which is freedom. In doing this, we would have an opportunity at profitable the sport of Bitcoin Sabotage and defeating our enemy, the state.